Cloud adoption keeps growing, but compliance risk grows with it. As organizations move data and workloads across public cloud, SaaS platforms, and hybrid environments, small control gaps can lead to audit failures, fines, or breaches.
Cloud security compliance is not the same as cloud security. Compliance shows that required controls are in place. Security focuses on reducing real risk. Strong cloud programs need both.
This guide explains cloud security compliance in plain language, covers the major frameworks, and gives you a practical checklist you can apply across modern cloud environments. For many teams, that work becomes more effective when it aligns with a broader security planning approach from the start.
What Is Cloud Security Compliance?

Definition and Purpose
Cloud security compliance means aligning your cloud systems, data handling, and operating processes with required standards, laws, or contractual obligations.
Its main goals are to:
- protect sensitive data
- reduce legal and audit risk
- improve consistency across cloud environments
- prove that security controls are working
Compliance vs Security
Compliance is a defined requirement. Security is the broader effort to reduce threats.
Compliance focuses on whether controls exist, are documented, and can be proven during an audit. Security focuses on whether those controls actually reduce the chance and impact of an attack.
A company can pass an audit and still have weak real-world security. That is why compliance should support security, not replace it.
Why Cloud Environments Increase Risk
Cloud environments change fast. Resources are created, updated, and removed through code, APIs, and automated pipelines. That speed helps the business, but it also creates risk.
Common cloud risk drivers include:
- poor visibility across accounts and services
- misconfigurations
- excessive permissions
- unclear ownership
- multi-cloud complexity
- rapid deployment without proper review
Shared Responsibility Model
Cloud compliance depends on understanding who is responsible for each control.
IaaS vs PaaS vs SaaS Responsibilities
The responsibility split changes by service model.
IaaS: The provider manages the underlying infrastructure, while the customer manages operating systems, workloads, identities, configurations, and data.
PaaS: The provider manages more of the platform, but the customer still owns application security, access control, data protection, and service configuration.
SaaS: The provider manages most of the stack, but the customer still controls user access, tenant settings, data governance, and how the service is used.
Provider vs Customer Responsibilities
In simple terms, the provider is responsible for security of the cloud, and the customer is responsible for security in the cloud.
Customer responsibilities usually include:
- identity and access management
- data classification
- encryption choices
- logging and monitoring
- regulatory alignment
- incident response
- evidence collection
Common Gaps and Risks
The biggest cloud compliance failures often come from unclear ownership.
Common gaps include:
- admin access that is too broad
- misconfigured storage or network settings
- poor backup testing
- incomplete logging
- weak vendor oversight
- missing audit evidence
Key Frameworks and Standards

Organizations usually combine a general control framework with industry-specific or regulatory requirements.
NIST SP 800-53 and 800-144
NIST SP 800-53 provides a broad set of security and privacy controls. It is useful for building a formal internal control structure.
NIST SP 800-144 focuses on cloud-specific security and privacy issues in public cloud computing.
ISO/IEC 27001
ISO 27001 is a widely used standard for building an information security management system. It is useful for organizations that want structured governance, risk management, and continuous improvement.
CSA Cloud Controls Matrix
The CSA Cloud Controls Matrix is designed specifically for cloud security. It is especially useful for cloud assessments, vendor reviews, and control mapping across multiple frameworks.
CIS Controls v8.1
CIS Controls help teams prioritize practical security improvements. They are useful for turning broad compliance goals into clear operational actions.
SOC 2
SOC 2 is commonly used by service providers that need to show customers they have appropriate controls for security and related trust principles.
GDPR, HIPAA, PCI DSS
These are regulatory or sector-specific requirements:
- GDPR applies to personal data protection
- HIPAA applies to protected health information
- PCI DSS applies to payment card data
Table 1: Framework Comparison
| Framework | Focus Area | Best Use Case | Industry |
| NIST SP 800-53 | Broad control catalog | Building a formal security control program | Government, enterprise, regulated sectors |
| NIST SP 800-144 | Cloud security guidance | Public cloud risk management | Cross-industry |
| ISO/IEC 27001 | Security management system | Governance and certification programs | Cross-industry |
| CSA CCM | Cloud-specific controls | Cloud assessments and control mapping | Cloud-first organizations |
| CIS Controls v8.1 | Prioritized safeguards | Practical security improvement | Cross-industry |
| SOC 2 | Service assurance | Demonstrating control effectiveness to customers | SaaS, service providers |
| GDPR | Privacy and personal data | EU-related data processing | Cross-industry |
| HIPAA | Health data protection | Healthcare workloads | Healthcare |
| PCI DSS | Payment data security | Cardholder data environments | Retail, fintech, payments |
Cloud Security Compliance Checklist

Governance and Risk Management
Start with governance because every other control depends on ownership and accountability.
Checklist:
- define cloud security policies
- assign control owners
- maintain a cloud risk register
- document exceptions and compensating controls
- review policies on a set schedule
Asset Inventory and Data Classification
You cannot secure or audit assets that you do not know exist.
Checklist:
- maintain inventory across cloud accounts and services
- identify data owners
- classify data by sensitivity
- tag assets by function, owner, and environment
- track data flows across cloud and third parties
Identity and Access Management (IAM)
IAM is one of the most important control areas in cloud compliance.
Checklist:
- enforce MFA for all users
- apply least privilege
- review access regularly
- control privileged accounts tightly
- secure machine identities and service accounts
- log high-risk access events
In practice, this may include centralized identity controls through platforms such as Microsoft Entra ID, especially when organizations need stronger policy enforcement across cloud and SaaS environments. A stronger zero trust model can also help reduce access risk in cloud environments.
Secure Configuration and Hardening
Cloud defaults are not enough for compliance.
Checklist:
- create secure baselines for systems and services
- disable risky default settings
- prevent unintended public exposure
- scan for configuration drift
- review infrastructure-as-code before deployment
Network Security and Segmentation
Cloud networks should be segmented based on risk and business purpose.
Checklist:
- separate production from development and test
- restrict east-west traffic
- use deny-by-default rules
- protect remote and administrative access
- review internet-facing assets often
Data Protection and Encryption
Most compliance programs require strong data protection controls.
Checklist:
- encrypt sensitive data at rest and in transit
- manage keys securely
- define retention and deletion rules
- protect backups
- review cross-border data handling requirements
Logging, Monitoring, and Detection
Good compliance depends on strong records and visibility.
Checklist:
- enable audit logging across cloud services
- centralize logs securely
- monitor admin actions and access events
- define alerts for high-risk activity
- retain logs according to policy and legal needs
Vulnerability and Patch Management
Weak patching can quickly become both a security issue and an audit issue.
Checklist:
- scan workloads and images regularly
- prioritize high-risk exposures
- define remediation timelines
- track remediation evidence
- remove unsupported software where possible
For example, some teams combine exposure analysis from platforms like Tenable with cloud and network controls from providers such as Palo Alto Networks to improve both remediation speed and audit visibility.
DevSecOps and Change Management
Compliance should be part of the build and release process.
Checklist:
- review code and infrastructure changes
- scan dependencies and secrets in CI/CD
- require approvals for high-risk production changes
- document emergency changes and rollbacks
- keep change records for audit use
Backup and Disaster Recovery
Recovery readiness is a core compliance concern.
Checklist:
- define recovery objectives
- automate critical backups
- test restores on a schedule
- protect backup access
- document recovery results
This often includes tested backup workflows through tools such as Veeam when organizations need stronger recovery evidence for audits and resilience planning.
Incident Response and Breach Handling
Every cloud program should have cloud-specific incident procedures.
Checklist:
- maintain incident response playbooks
- define escalation paths
- preserve logs and evidence
- document notification requirements
- test response procedures regularly
Third-Party Risk Management
Compliance does not stop at your own environment.
Checklist:
- review vendor security documentation
- assess critical service providers
- verify data handling commitments
- monitor third-party changes that affect control coverage
- include cloud vendors in risk reviews
Continuous Compliance and Auditing
Cloud compliance should be continuous, not just annual.
Checklist:
- map technical checks to framework controls
- automate evidence collection where possible
- review control health regularly
- track remediation and exceptions
- perform internal readiness reviews before audits
Control Mapping Strategy
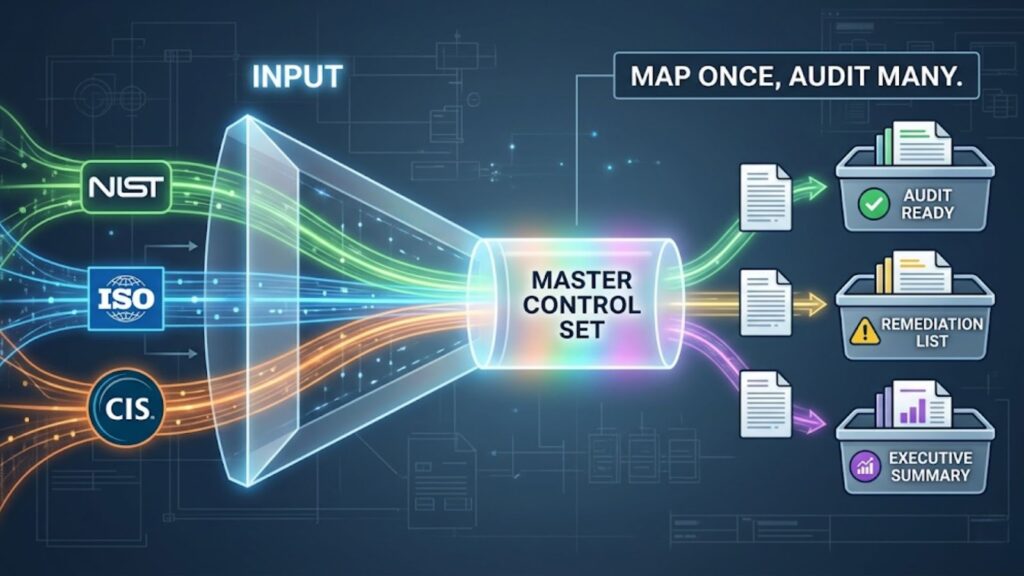
A unified mapping strategy helps reduce duplicate work.
Mapping NIST, ISO, and CSA CCM
Use one internal control set, then map it to multiple frameworks. This makes audits easier and reduces repeated evidence gathering.
Using CIS Controls for Prioritization
CIS Controls help teams decide what to address first. They are especially useful when a program needs quick improvement in high-impact areas like IAM, hardening, logging, and vulnerability management.
Adding Regulatory Layers
After mapping your core framework, add regulatory requirements based on the data you handle.
For example:
- add GDPR for personal data
- add HIPAA for health data
- add PCI DSS for payment environments
Table 2: Control Mapping Matrix
| Control Area | NIST | ISO | CSA CCM | CIS |
| Governance and Risk | RA, PL, PM | Clauses 4–10 | GRM | 17 |
| Asset Inventory | CM | Annex A | AIS | 1, 2 |
| IAM | AC, IA | Annex A | IAM | 5, 6 |
| Secure Configuration | CM, SI | Annex A | CCC | 4, 7 |
| Network Security | SC, AC | Annex A | IVS | 12, 13 |
| Data Protection | SC, MP | Annex A | DSP, EKM | 3, 11 |
| Logging and Monitoring | AU, SI | Annex A | LOG | 8 |
| Vulnerability Management | RA, SI | Annex A | TVM | 7, 18 |
| Incident Response | IR | Annex A | SEF | 17 |
| Backup and Recovery | CP | Annex A | BCR | 11 |
| Third-Party Risk | SR | Annex A | STA | 15 |
Tools and Automation for Compliance
Automation helps cloud compliance scale.
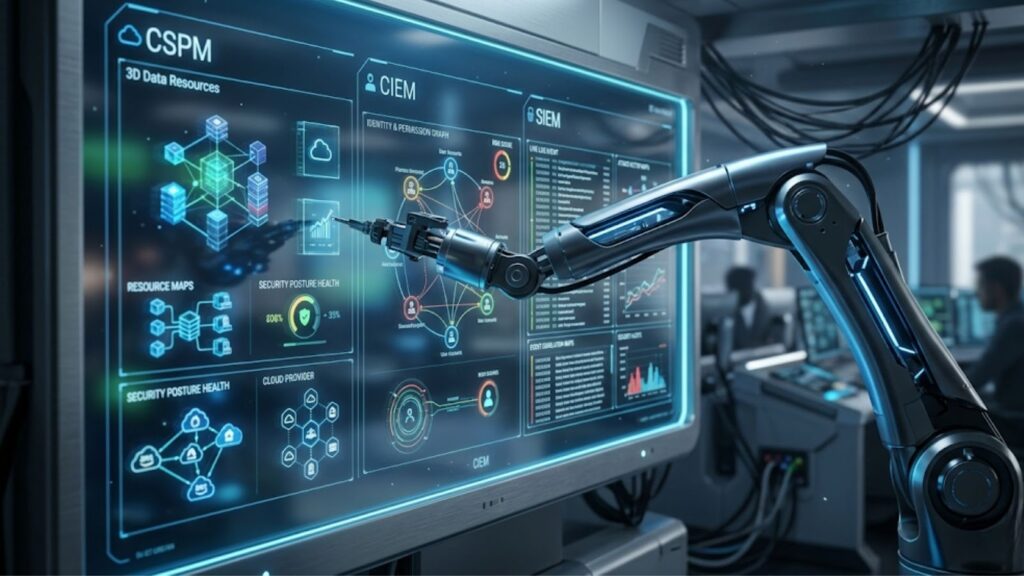
CSPM
Cloud Security Posture Management tools scan for misconfigurations, policy drift, and failed control checks.
CIEM
Cloud Infrastructure Entitlement Management tools focus on permissions, privilege sprawl, and identity risk.
SIEM and SOAR
SIEM helps centralize logging and detection. SOAR helps automate response and evidence handling.
Evidence and Audit Readiness

Audit success depends on having complete, organized proof.
Required Evidence Types
Common evidence includes:
- policies and standards
- risk assessments
- asset inventories
- access reviews
- configuration records
- change tickets
- vulnerability reports
- incident records
- backup test results
- vendor attestations
Continuous Monitoring vs Point-in-Time Audit
Point-in-time audits only show whether controls worked during one review period. Continuous monitoring shows whether controls stay effective as cloud environments change.
For cloud systems, continuous monitoring is the stronger model because it improves visibility, reduces audit stress, and catches drift earlier.
Common Audit Failures
Common reasons cloud audits fail include:
- incomplete asset inventory
- weak access reviews
- missing change evidence
- poor data classification
- inconsistent logging
- untested recovery plans
- unclear vendor oversight
Common Challenges in Cloud Compliance

Multi-cloud Complexity
Different providers use different services, settings, and logging models. That makes consistent control enforcement harder.
Misconfigurations
Misconfigurations remain one of the most common cloud compliance problems because they can expose systems quickly.
Lack of Visibility
Without a clear view of assets, identities, and data flows, compliance becomes difficult to prove.
Responsibility Confusion
Many issues start when teams assume someone else owns a control.
Best Practices for Cloud Security Compliance

Zero Trust Approach
Apply least privilege, verify access, segment critical systems, and reduce standing trust wherever possible.
Automation-First Compliance
Use automated checks, policy enforcement, and evidence collection to reduce manual effort and improve consistency.
Shift-Left Security
Move security reviews into design, development, and deployment workflows.
Continuous Monitoring
Treat compliance as an ongoing operational activity, not a once-a-year project.
Need Help Applying This Checklist to Your Infrastructure?
For organizations turning compliance requirements into real infrastructure decisions, Catalyst Data Solutions Inc supports secure, vendor-agnostic IT planning and deployment.
FAQs
What is cloud security compliance?
Cloud security compliance is the process of meeting security, privacy, and governance requirements for cloud systems through documented controls, monitoring, and audit evidence.
Which framework should I follow first?
Most organizations start with NIST or ISO 27001 for structure, then use CSA CCM for cloud-specific mapping and CIS Controls for prioritization.
Is compliance enough for security?
No. Compliance provides a baseline, but security also requires active risk reduction, monitoring, and response.
How often should cloud compliance be audited?
Formal audits may be annual, but internal control review and monitoring should be continuous.
What is shared responsibility in cloud?
It means the cloud provider secures parts of the service, while the customer secures identities, data, configurations, and how the service is used.
How do you automate cloud compliance?
Use CSPM, CIEM, SIEM, automated policy checks, and CI/CD controls to detect drift and collect evidence continuously.